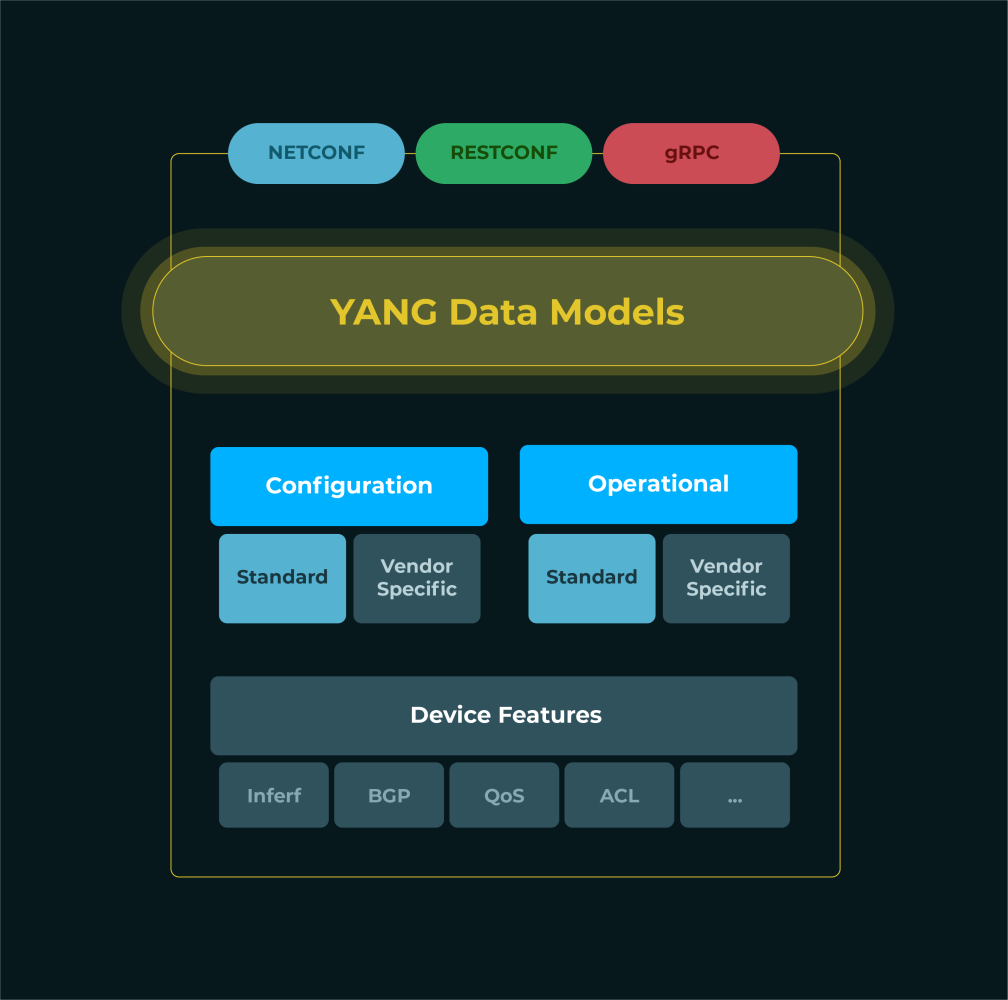
YANG (Yet Another Next Generation) is a data modeling language that is used to define the structure of configuration data for network devices and network services.
It allows organisations to model and configure network and security services in a machine-readable format. The YANG models can then be used to generate code or CLI commands that can be executed on network devices to configure the network services.
By using YANG to configure network and security services, network administrators can ensure that the configurations are consistent and well-structured, making it easier to manage and maintain the network.
Here are the steps to configure network and security services using YANG:
Develop the YANG model:
The first step is to develop a YANG model that defines the configuration data required to configure the network and security services. The YANG model defines the structure of the data, the data types, and the relationships between the data elements.
In DNA this is extremely easy: You just need to define the blocks you would like to use and include this in the template you have. You can have as many templates, for different devices or vendors or models.
You will assing to every vendor or model a specific template that needs to be used.
Changing on part of the configure, for example a block, will automatically apply it to any other template that is using this block.
Compile the YANG model and generate the code:
Once the YANG model is developed, it must be compiled into a format that can be used by network devices.
In DNA this is already prepared. It’s just one click of a button to have the configuration created.
You can also include this as part of a more complex workflow, more on this later.
Deploy the code:
The code generated from the YANG model can then be deployed on the network devices.
The code can be deployed directly on the devices, using the DNA workflow designer or as part of the Service Provisioning module that is available within DNA.
Also in case you would want to release a new version of a specific part of the configuration, for example one specific block, you can with a few clicks reconfigure all devices involved.
Validate the configuration:
After the code is deployed, it is important to validate the configuration to ensure that the network and security services are configured correctly.
In DNA you can create workflows that can do this for you, based on your validation criteria to see if the service is functioning as need. It’s even possible to schedule these checks for a period of time, which your operational team will love since they are the ones dealing with “early life failures”.
Service Provisioning
The above text is giving you a simple overview of what you can do with yang templates. Even if you might not want to 100% automate it, it’s still very usefull to generate configuration based on a fixed standard.
But with DNA there is the posibility to create much larger provisioning workflows. Any step you can think of can be executed using a module that is available in DNA. The modules can be (visually) linked together, based on specific conditions, to manage your end to end service provisioning.
for example:
- When a device becomes available in the network, for example when it gets plugged in, the event manager can send a notification.
- This will trigger a workflow to start doing some basic checks. Maybe a ping followed by retrieving the base configuration of the device to get some initial parameters.
- Then it connects to your CRM and CMDB solution to retrieve more information about this specific service, to define how it should be configured as it was ordered.
- It generates the new configuration, with all services on top of it, and stores the configuration.
- Then it will reconfigure the device, but maybe also some other parts of the network, in order to make the service work as it supposed to be working.
- It then can test the service and based on the outcome update any upstream system and inform the teams involved.
