
Category: Automation
The five stages of network and security autonomy
If you like SaltStack, you will ❤️ DNA
Already like SaltStack? Don’t know where to start? Or maybe you miss something?
Maybe have a look at what we do…

Security is everyone’s responsibility
The overall security of your network and applications is getting more and more of a hot topic. Especially for big organizations and governments, network security is vital but at the same time getting increasingly complex.
Security is not just the responsibility of a specific individual or department in an organization, but it is a shared responsibility of every person within the organization, including employees, contractors, and even customers.

Configure your network & security infrastructure using YANG templates
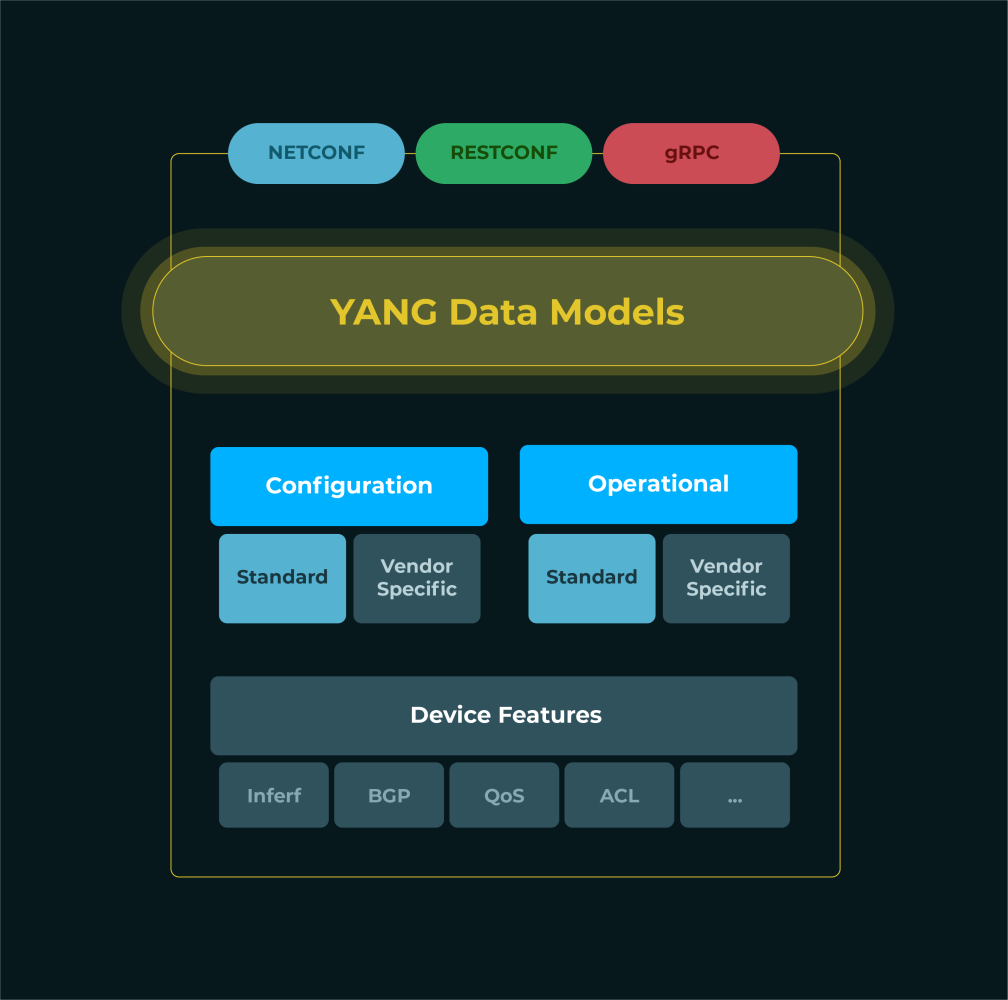
YANG (Yet Another Next Generation) is a data modeling language that is used to define the structure of configuration data for network devices and network services.
It allows organisations to model and configure network and security services in a machine-readable format. The YANG models can then be used to generate code or CLI commands that can be executed on network devices to configure the network services.
By using YANG to configure network and security services, network administrators can ensure that the configurations are consistent and well-structured, making it easier to manage and maintain the network.
How to start with RPA as a developer?
Were you thinking about starting with RPA? Today we prepared an article that will respond to all your questions!

IT Asset Management is the cornerstone of your IT function
There is a good reason why ITIL is spending a dedicated part on IT Asset Management (ITAM). It’s supposed to underpin everything that you do as an IT function.
Not having the correct level and correctness of your asset management can cause not only delays on your day-to-day operations, it can also cost you a lot of extra money and can expose you to all sorts of data or security breaches.

How does RPA integration work?
Building an RPA solution, unfortunately, doesn’t fit the idea of a single house or multiple same houses either. RPA is a bit specific. Sometimes you have all the requirements in advance but still, there might be minor changes during the journey. As well the user interface of third-party applications might change. But usually, there are no big changes in the business processes we need to automate. And that’s the power of RPA too, remember? You don’t need to adjust the business process anyhow.
External provider’s systems integration
Robotic Process Automation (RPA) is a technology used for any organization or company that is stuck with an old outdated application to manage their process or in case a high amount of integration is needed with external systems, portals, or applications running on someone’s PC.

